Taig is a Chinese iOS developer team who has proved itself trustworthy, providing a fully working jailbreak app for all iPhone users.
Taig jailbreak is for iOS 8 and is an untethered jailbreak utility that works on 32-bit devices without needing to be reactivated when the device is restarted. It has also been proven to be a safe and secure jailbreak to use. For more details on how to download Taig jailbreak, keep reading.
Supported Devices:
Taig works on the following devices:
- iPhone 4S, 5, 5C, 5S, 6, 6 Plus
- iPad Air, Air 2
- iPad 2, 3, 4
- iPod Touch 5G
Important Points:
Before you install Taig jailbreak, read these important points:
- It is compatible with both Mac and Windows operating systems
- It is an untethered jailbreak
- You must back your device up before you attempt to install Taig jailbreak
- Disable Find my iPhone/iPad, your passcode and/or Touch ID; these can be reactivated after the jailbreak
- You must also check the latest iOS 8 Jailbreak apps available which might be more stable and have a better success rate in jailbreaking your iOS device.
Content Summary
How to Jailbreak with Taig app on Mac:
- Download Taig jailbreak to your Mac using the download button above (version 1.1.0)
- Connect your Mac and device using the right cable
- Open the location of Taig jailbreak on your Mac and double-click on the .dmg file; when asked to, move it to your Applications folder.
- Right-click the Taig app and then click Open > Open
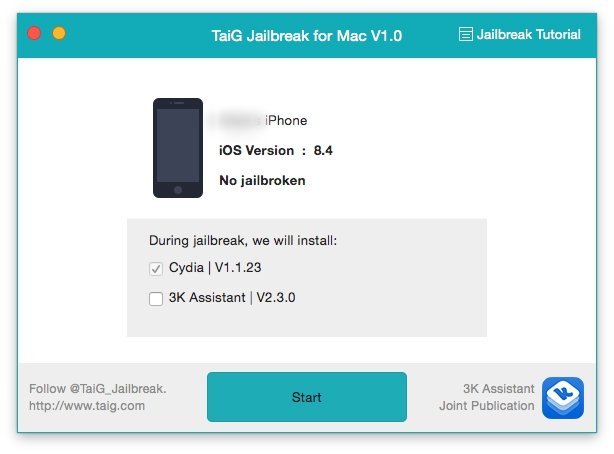
- Wait for Taig jailbreak to recognize your device; when it does, disable the option to install 3K Assistant 2.3.0 ( this is the Taig App store, and you will see it just below Cydia )
- Click on Start
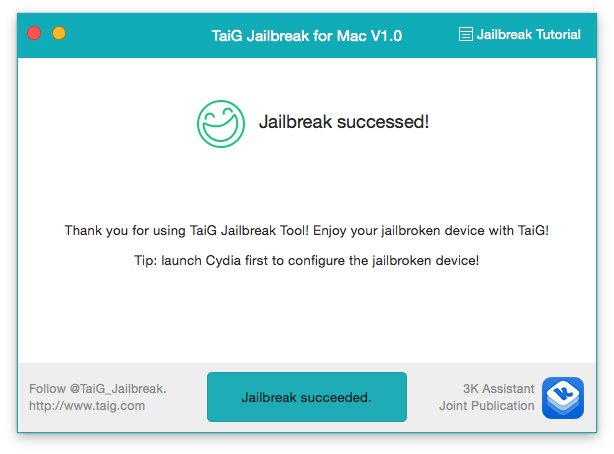
- Leave your device alone, it will reboot a number of times and, once complete; you will see the icon for Cydia on the home screen. You will also see the message, “Jailbreak Succeeded” on the jailbreak tool
How to Jailbreak with Taig on Windows:
- Download Tag to your Windows PC and extract the file contents (version 2.4.5 )
- Connect your iPhone or iPad to your Windows PC
- Find the Taig.exe file and right-click it; select “Run as Administrator” to open it
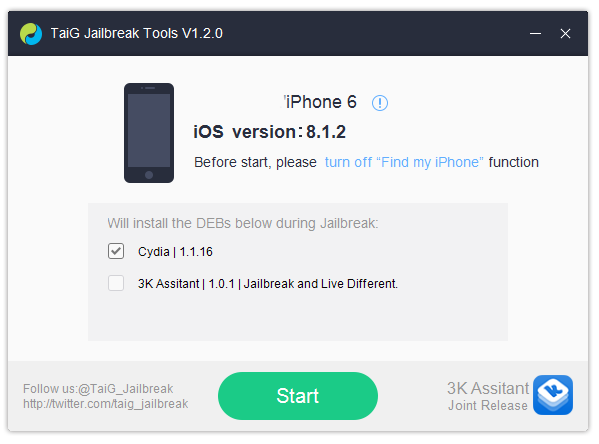
- Wait until Taig has detected your device and then disable the option to install the app store, 3K Assistant, which you will see under Cydia
- Click on Start and wait; when your device reboots itself, the Cydia icon should be on the home screen, and the jailbreak is complete.
Regardless of which OS you use, when the jailbreak has finished, open Cydia and set it up for first-time use. Then you can start using it to download your favorite tweaks.
Troubleshooting Guide:
Despite the updates, there are still some common errors with Taig jailbreak, and we are going to discuss those now, along with solutions for fixing.
- Error 1101/Stuck at 20%
Some people report Taig getting stuck at 20%, and the easiest way to fix this is to downgrade iTunes and try again.
- Injecting/Stuck at 60%
If you get this error, reboot your device and your computer. Launch Taig in Administrator mode on your computer and try again. You can also do a hard restart – press the Home and Sleep/Wake buttons together until you get a blank screen followed by the Apple Logo
- Apple Driver Not Found
Make sure you are using the latest iTunes version; otherwise, the jailbreak may not be able to complete. Open iTunes, click Help > Check for Updates and follow the onscreen instructions. Try the jailbreak again.
- Your Tweaks Don’t Work
Go into Cydia and download Taig 8.1.3-8X Untether package. This fixes the Cydia substrate; when you open Cydia, you will see an Essential Upgrade message – tap Complete Upgrade and the newest packages will be installed. Also, check that the tweaks you are downloading are compatible with your iOS version.
- Your App Icons Disappear
Follow the steps above to download the latest Untether package from Cydia to fix this issue. Again, you must tap Complete Upgrade n the message that appears when you open Cydia again
Other TaiG Errors:
- Jailbreak Failed Message
Disable Wi-Fi on your device and try the jailbreak again
- Error 1102
Enable Airplane mode and make sure you disabled passcode and Touch ID
- Error 1103
The Taig jailbreak file is most likely corrupted; re-download it from the official source and try again.
- Error 104
Try a different USB port on your computer or, if you use a USB hub, bypass it and connect your device directly. If the problem persists, try another computer.
- Error 1105
Disable your firewall and anti-virus software temporarily; make sure you reenable them once the jailbreak is complete.
- Storage Almost Full Message Following Jailbreak
Run Cydia, set it up for first use, and wait; the error should clear.
Are you going to use Tag jailbreak on your iOS 8 device? Tell us how you get on with it, and get more news and developments by following us on Facebook.

Hey, i want just ask you something. I have iOS 8 TaiG Jailbreaked on iPhone 4S, I had the Facebook ++ tweak, which has a chat heads and no messenger was needed. Now i don’t have in this tweak chat heads…only messages…it probably updated and now it’s not working…
Can I downgrade the tweak to previous version?
Or do you know some tweaks that help me sort a problem with chat heads? And something for quick reply for Facebook? like IMN?
sorry for my english, it’s not perfect ????
Thank you!
think you should download something like the app installers , Emus4U or TweakBox app. It can solve your problem . No jailbreak needed for that.